McAfee Phishing Email Investigation
I received this email the other day and decided to investigate it. I have received several versions of this in the past couple of months.
Note: These types of investigations require caution. Accidently left-clicking on links on your actual machine inside an unprotected browser can result in disaster. For most of the steps below, everything was done within an isolated kali linux virtual machine.
![]()
Let's see how this phishing attempt works.
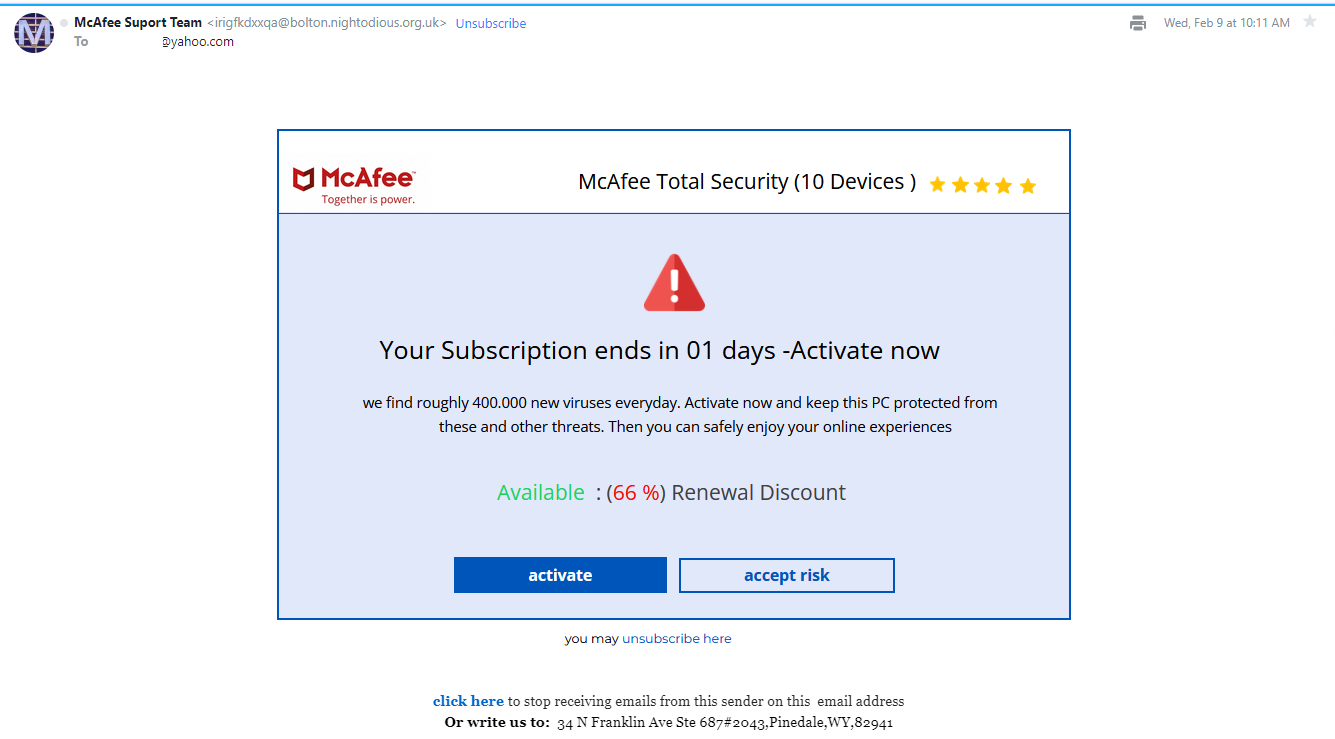
Here is the email itself.
Looking at the raw headers, I see the originating IP and that dkim, spf, and dmarc are all unconfigured (big red flag).
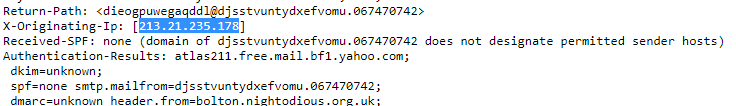
This IP is from Latvia. I'm pretty sure McAfee wouldn't host its email servers in Latvia.
Phishing emails usually hide links within images as is the case with this example. Whether you click on 'activate' or 'accept risk' or anywhere within the confines of the image, it doesn't matter. It is all one, single image with a url behind it.
Simply right click the image > copy link address. Be careful not to left click the image and actually go to the website.
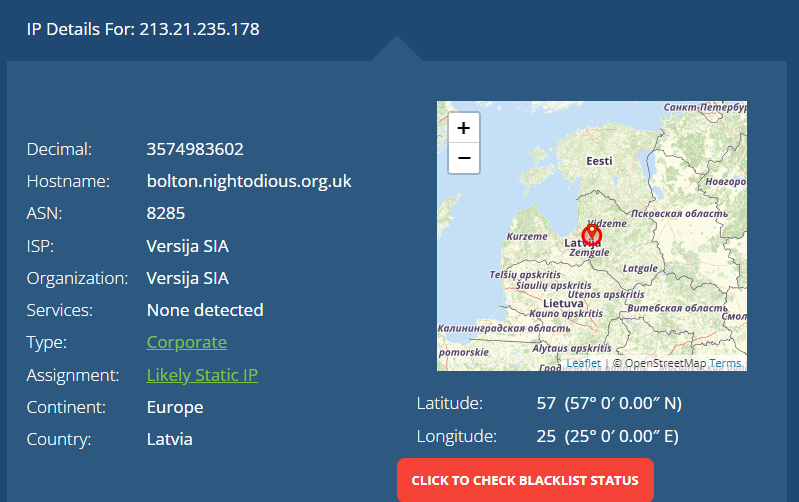
I scanned it using my urlscan tool at https://tmalinowski.com/scanurl/.
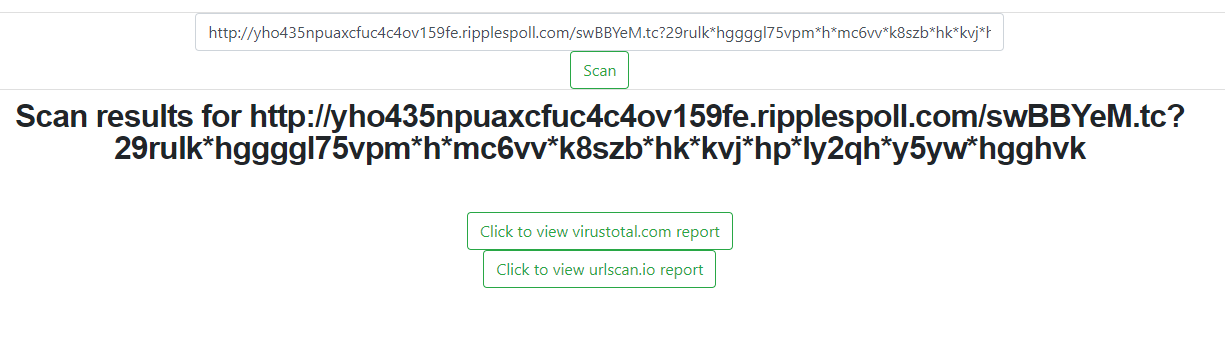
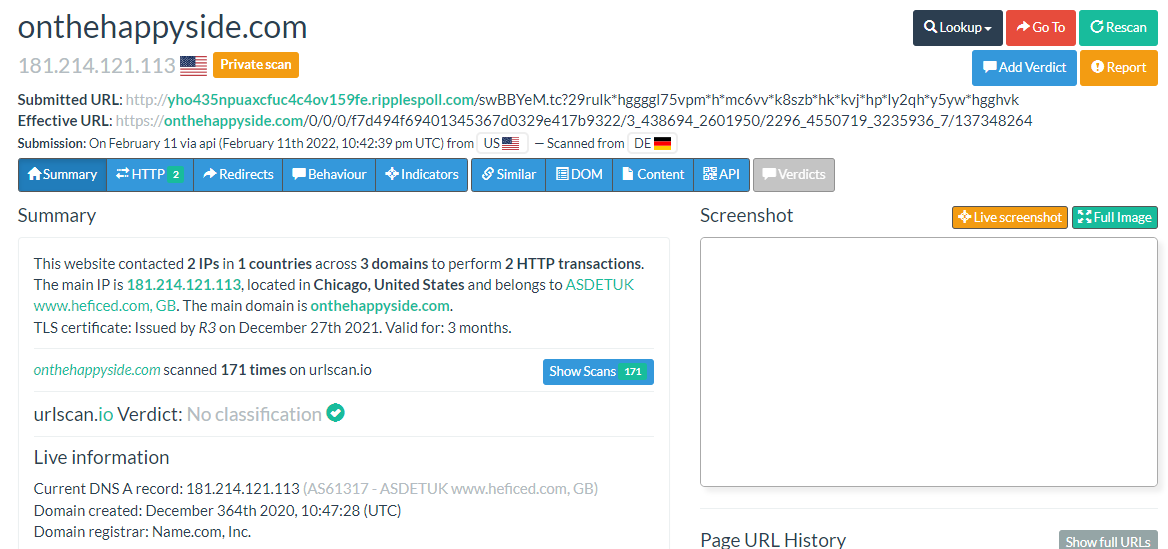
This is the urlscan.io results. Notice the effective url which is where you actually land after clicking the image (it leads to ripplespoll[.]com). After landing on ripplespoll[.]com you are redirected to onehappyside[.]com. Redirects are common in phishing, this helps avoid immediate blacklisting. A different original url may be used for each unique email. If one is blocked, there can be dozens, hundreds, or perhaps thousands of others.
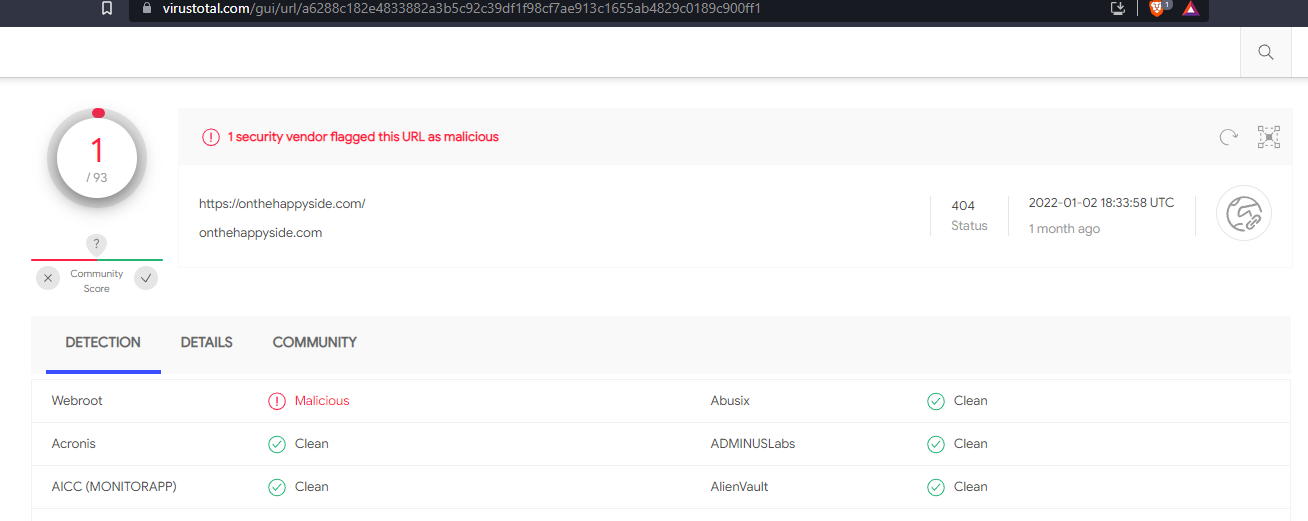
Here is the virustotal.com scan results for onthehappyside[.]com
Since urlscan doesn't go any further, doesn't give much else information in terms of scripts discovered, and results in a blank page (perhaps there is some linux host blacklisting on the malicious website's configuration) the next step is to check out the contents of the website using curl on a linux, kali virtual machine. The curl tool requests the website without the need for a browser or any graphical interpretation that a browser provides. It spits out raw html, website, code.
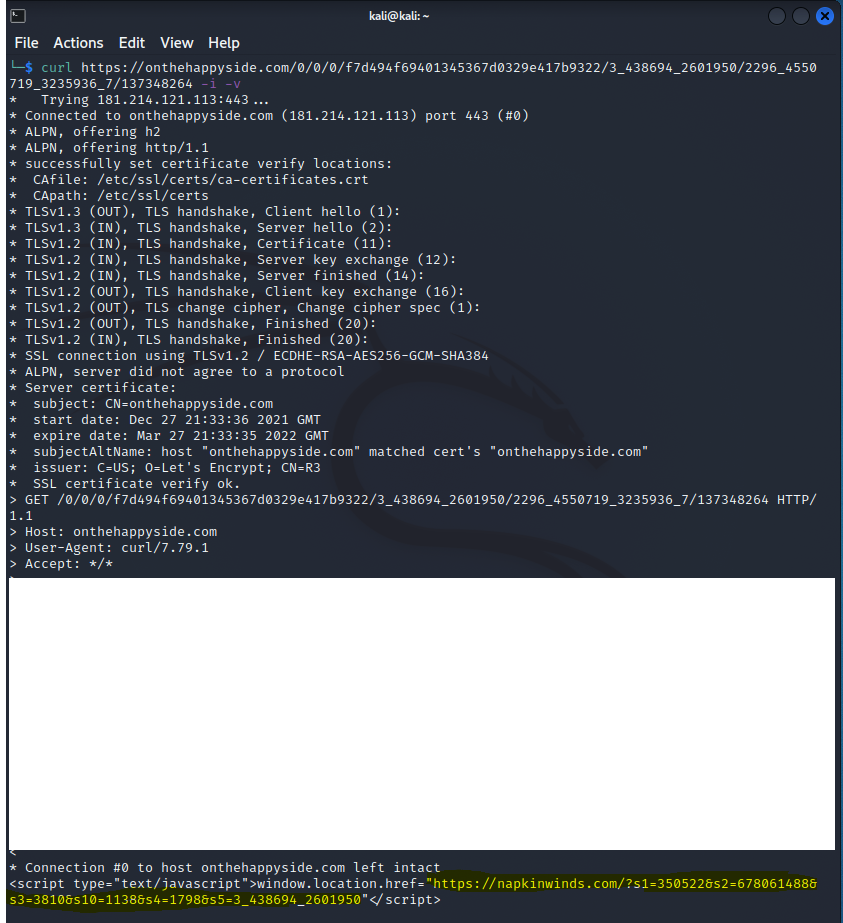
Notice at the bottom that there is indeed a script on the page, and it triggers upon landing there. It is a rediect to napkinwinds[.]com. Time to take this newly discovered url and run it through the scanner.
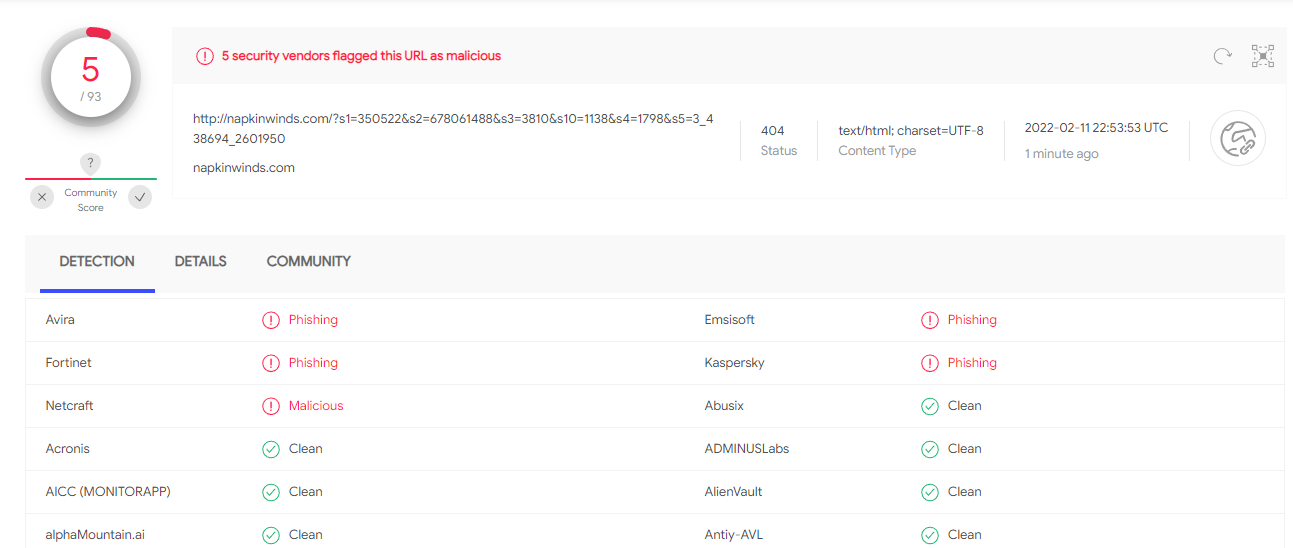
Here is the virustotal.com and urlscan.io results for napkinwinds[.]com
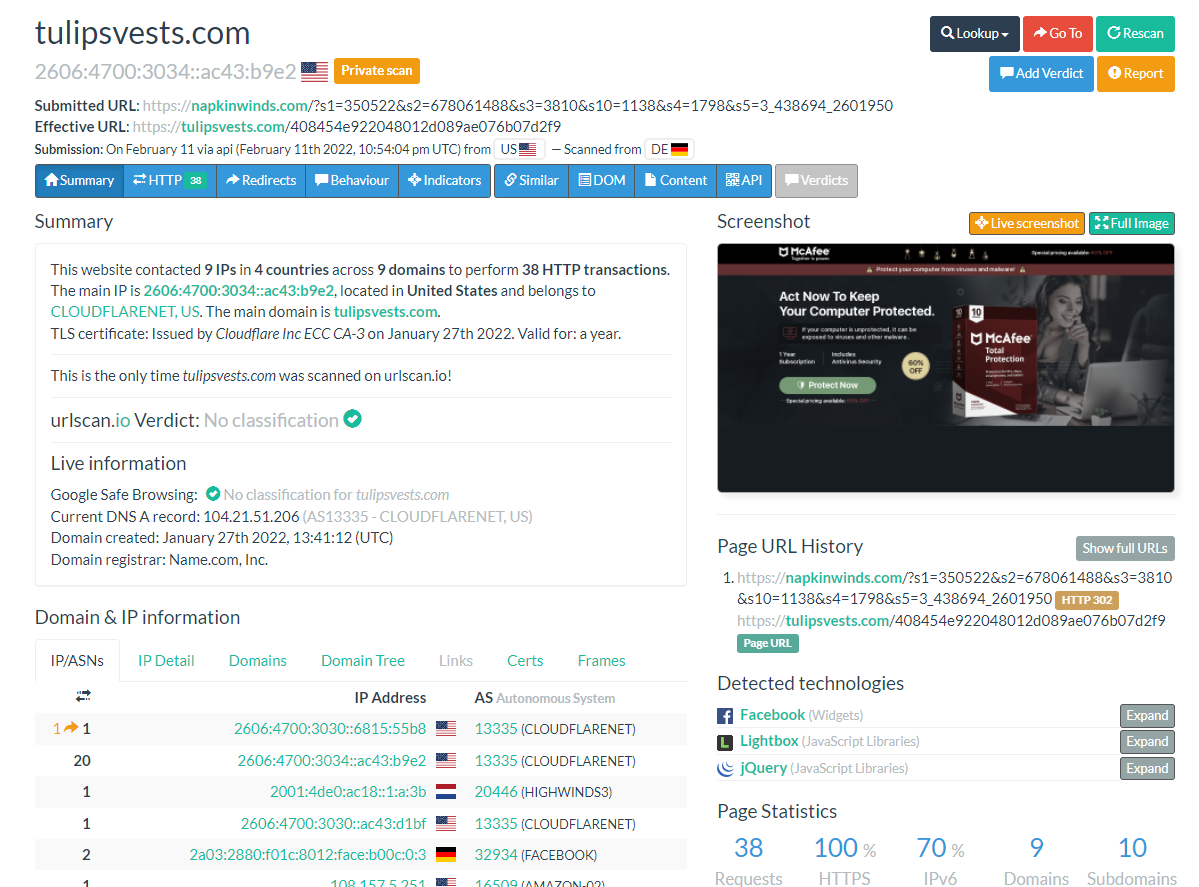
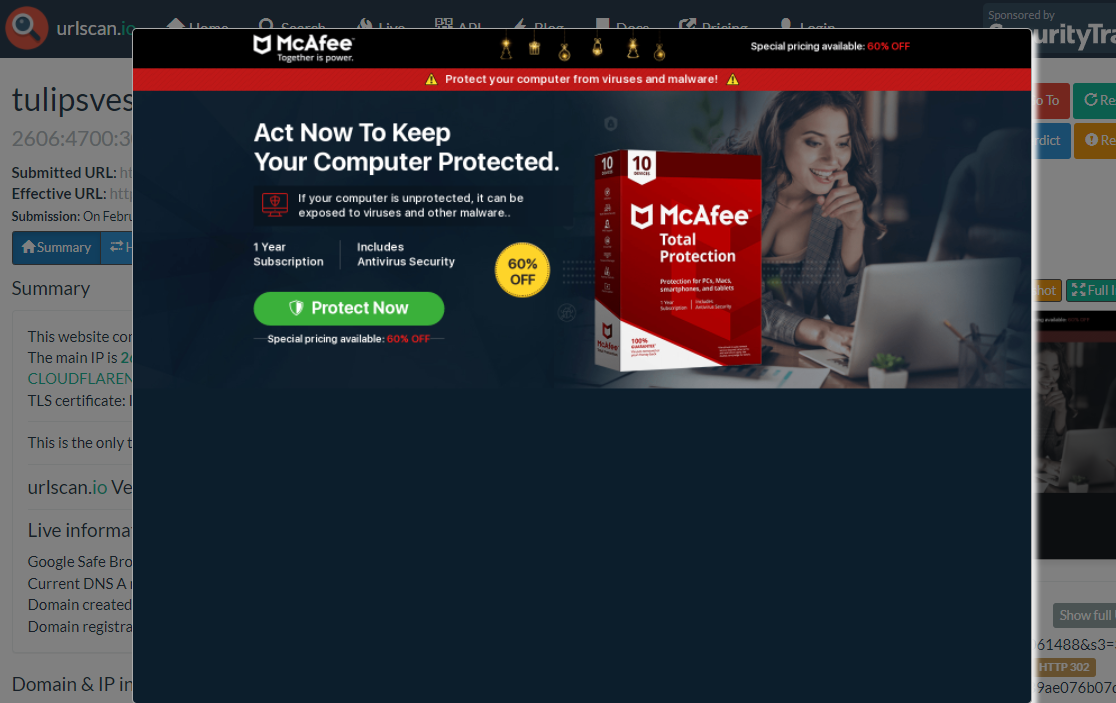
We see the final url, where the malicious actors want you to land and have set it up to trick you, is tulipsvests[.]com. The whole McAfee story plays out. To the untrained eye this looks legit. 60% off!
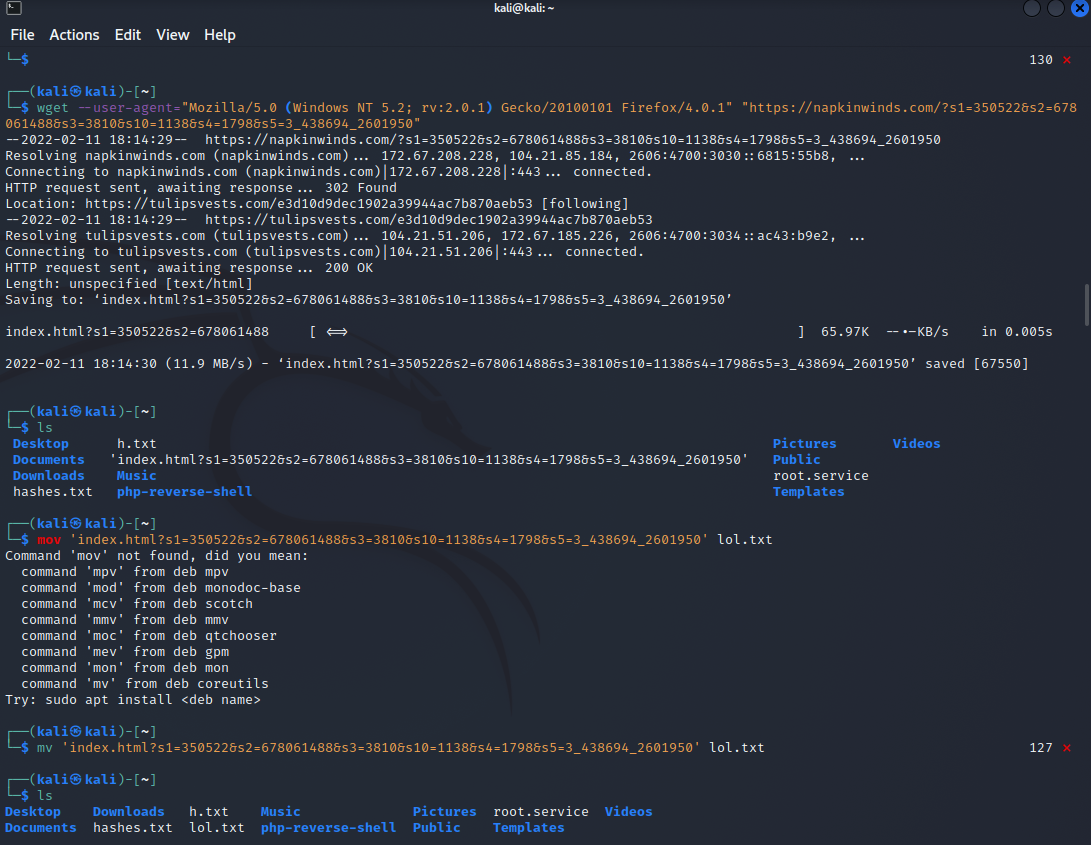
Naturally, the next step it to grab the raw html with the wget tool on the kali virtual machine. Notice that I am specifying a windows host. This may help bypass any protections against scans that the malicious actors have set up. The command downloads the page as if you went to it on a browser and right clicked > save page to a file. I then transfer the contents of the file, which was previously named 'index.html?s1=____________________', to lol.txt which you can see at the bottom.
Then I use the cat command to print out the text of the lol.txt file and you see that it is the actual code behind the tulipsvests[.]com website
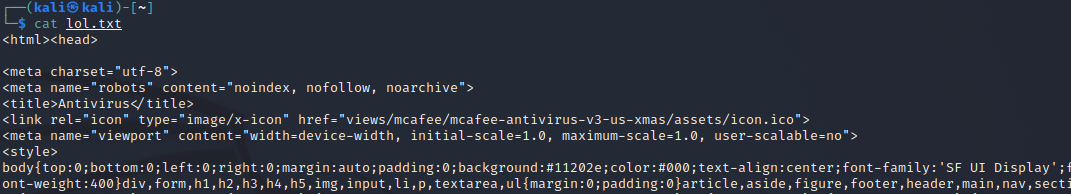
First thing I notice is that there is a javascript function connected to the green "Protect Now" button you see on the website. 'onclick="change()"' is javascript for whenever you click this link. In this case it's a button link.
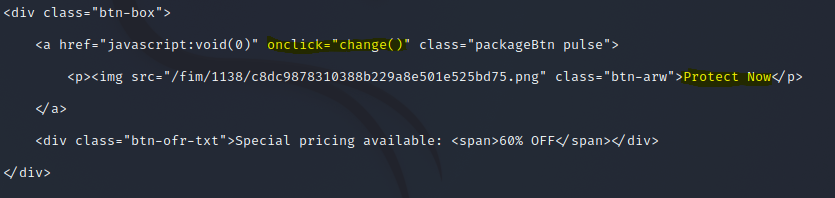
This is the javascript function, contained within an opening and closing <script> tag, it is calling upon clicking the button:
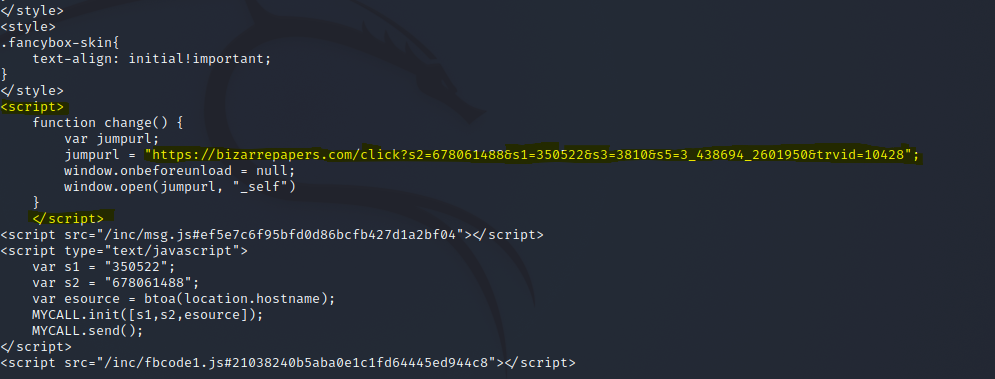
This script simply opens a new url, redirecting you to bizarrepapers[.]com. So if a victim clicks the green "Protect Now" button this new website opens up:
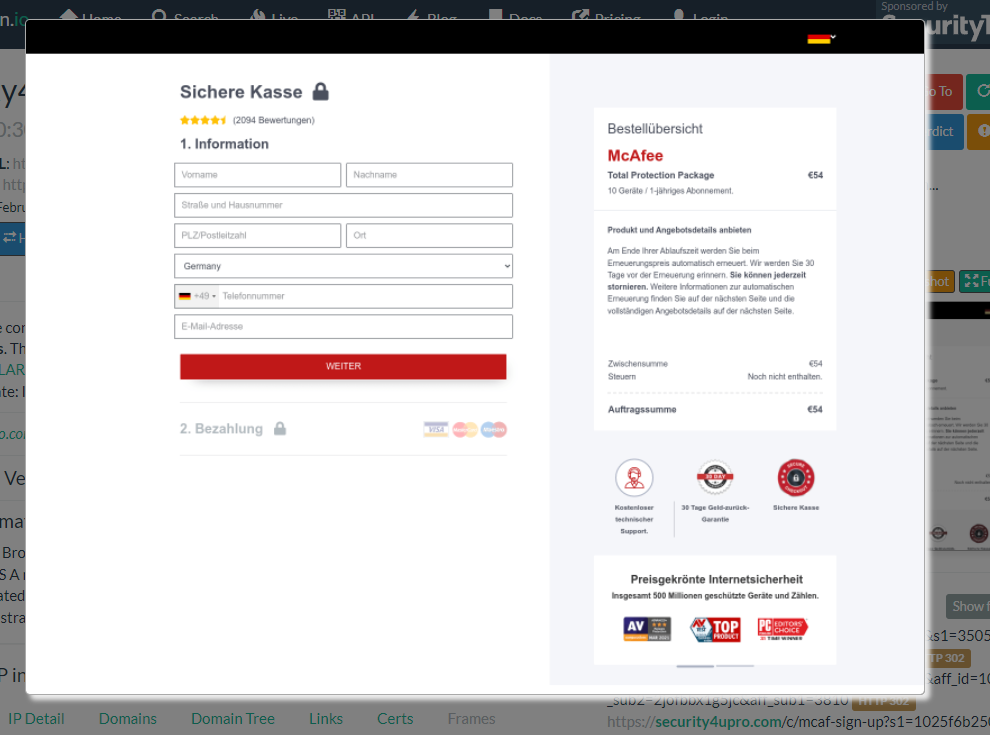
It is a fake payment page. The victim will enter their credit card information and their credentials will be stolen.
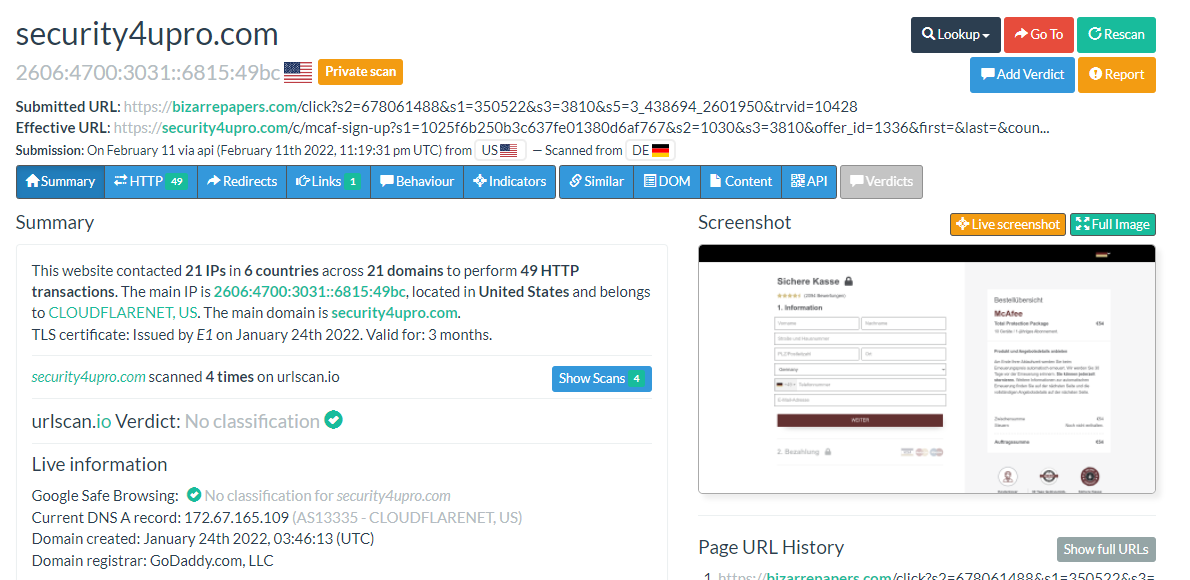
Here are the urlscan results. Notice the new effective url.
That is the entire story that the malicious actors have created. They attempt to scare you with a warning email that your subscription is ending, you click the image link in the email, get redirected a few times until landing on the fake website, click the protect now button, are sent to the fake payment page, and finally you give up your credit card information without even receiving the advertised product in the end.
But there is more. There is another interesting javascript snippet on the fake website. It loads a javascript file with the letters "fb" in the name.
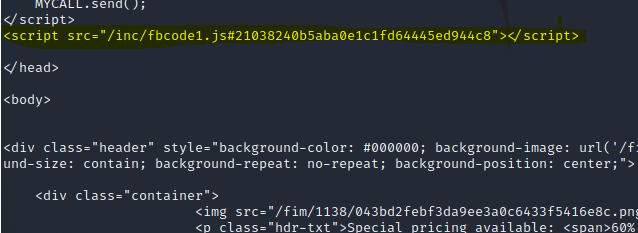
I run a wget and target that javascript source file specifically:
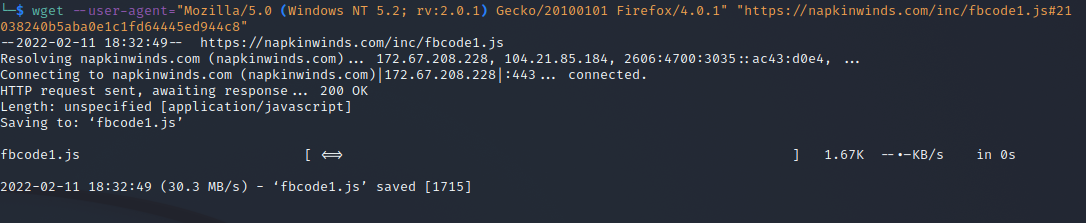
Again, I paste the results into a txt file called lol_fbcode.txt. Then I cat(print) out the contents:
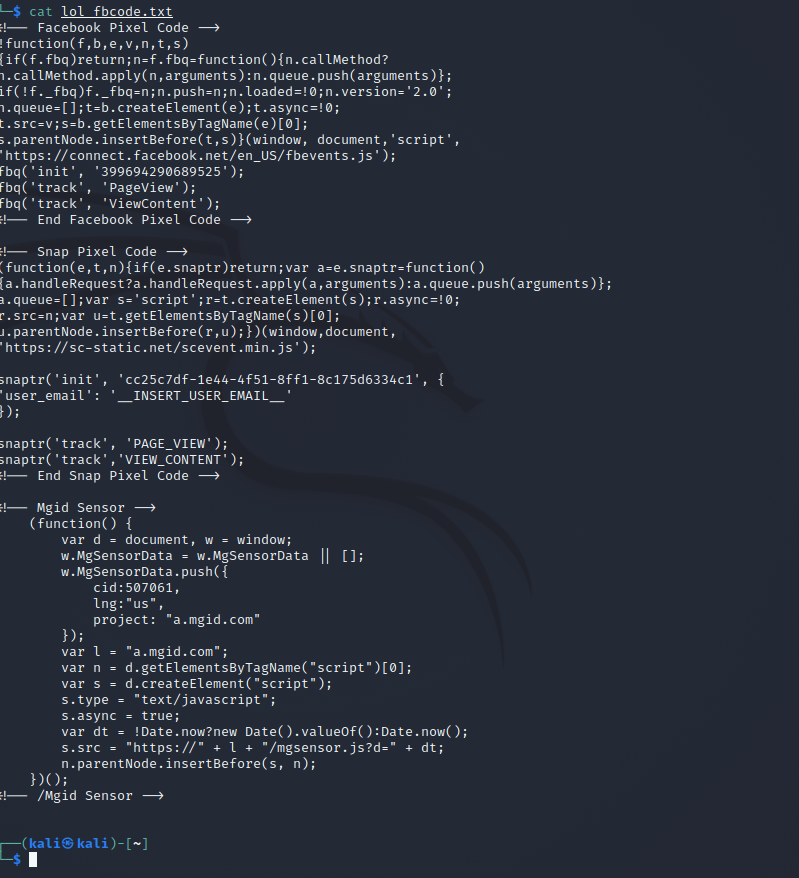
This javascript is loaded in the background and runs without the victim knowing. It seems to be utilizing facebook, snapchat, and mgid Pixel Conversion tracking. If I understand correctly, this means that this malicious website is being linked to in advertisements placed on facebook, snapchat, and other websites and the everytime a victim clicks on one of those advertisements and lands on this fake website, that "conversion" is being noted. Perhaps, the malicious actors want to know if their return on investing in advertisements on those websites is worth it.
Interesting.